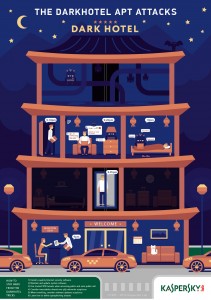
DarkHotel uses a malicious welcome pack
Kaspersky Lab recently released details of an espionage campaign called DarkHotel. The campaign has been running for 4 or more years, but up till now not much was known about it. The attackers target individuals once only; after the attackers have finished, they delete any evidence of their intrusion.
DarkHotel starts with a compromised Wi-Fi network in a hotel. Often the fact that the hotel network has been compromised is undetected for an extended period of time. The attackers target specific individuals; they usually know the surname and the room number of the victim.
A targeted individual will, on connecting to the Wi-Fi network, receive a message about a “welcome pack”. This welcome pack is supposedly from the hotel, but in reality, is designed to trick the victim into downloading malware. It does this by informing the victim that some software will need to be upgraded before proceeding.
The malware that is downloaded contains key logging functions as well as tools to steal sensitive information. The malware also trawls through the victim’s cached login credentials for browsers such as Chrome, Firefox and Internet Explorer. All information can be sent back to the attackers. Once the attackers are finished, they remove any traces of their work, and effectively vanish.
It is suspected that the attack is designed to glean confidential business information from the victim. The targets have mostly been executives; the hotels have often been fairly up-market, luxury hotels. According to Kaspersky, the industries the executives are from vary widely, and include pharmaceuticals, manufacturing and law enforcement areas.
There are ways to avoid becoming a victim of DarkHotel. The main precaution to take is care when using hotel (or any other) networks. In particular, if you receive a request to upgrade software when on a different network, check that the update is valid. Kaspersky also recommends that you use a VPN.
Scott Reeves
MailShark
Free anti-spam service
Free email filter service