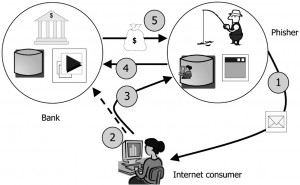
Phishing is simple but effective
A report written jointly by the University of California and Google looks at phishing and its success rate. The results are based on what Google observed on their Gmail accounts, but the results are still a revelation.
One of the aspects covered by the study was looking at the average time it took an attacker to login to a compromised account. According to the study, 20% of compromised accounts were accessed by the attackers within 30 minutes of the compromise. 50% of accounts were accessed within 7 hours.
Once an attacker gains access, they assess the value of an account. Some accounts are deemed to be of little importance, and are left alone. The average time an attacker takes to determine the importance of an account is 3 minutes.
A compromised email account may be used by the attackers to find the next phishing targets. Attackers go through the victim’s address book and send phishing emails to the contacts. According to Google online security, “People in the contact list of hijacked accounts are 36 times more likely to be hijacked themselves.”
Attackers sometimes locked out the victim by changing the password and retarded account recovery by changing other parts of a user account, such as secret questions and secondary email addresses. Another action the attackers carry out is to delete all emails and contacts. Doing this means that the victim (when they recover their account) cannot email his or her contacts to warn them of the scam.
The statistics around phishing pages are scary. Exceptionally accurate phishing pages will snare 45% of all users. Phishing sites that are very basic and lack the subtlety of more sophisticated phishing sites still succeed in 3% of all cases.
The message from the report underlines what many security professionals will say, which is that phishing looks very low tech and unsophisticated, but is very effective. Attackers are adept at inventing and adopting new methods of phishing.
One point to note is that these statistics are taken from Gmail accounts. Whilst these statistics are disturbing, it is important to remember that precautions exist and are effective. The main precaution to take is not to click on unverified links, and don’t enter in account credentials. Google also suggest you supply a phone number or secondary email address as backup, and to switch on 2 step authentication. In the case of SMEs, we (at MailShark) also recommend using an email filtering solution.
Scott Reeves
MailShark
Free anti-spam service
Free email filter service