Wait STOP – Are you installing Windows 10 or ransomware ?
People aren’t good at waiting for stuff, and with, computer users queueing up to download Windows 10, ransomware purveyors have started to move in.
Cisco’s security team has noticed a new spamming campaign attempting to spread the CTB-Locker ransomware using emails purporting to come from Microsoft, telling people they are ready to download Windows 10.
The emails mimic the actual Windows 10 messages Redmond is sending out (with some minor text mistakes) and have spoofed the originating address to read as update@microsoft.com, although the sender’s IP address can be traced back to Thailand. There’s also a Microsoft disclaimer, and a message claiming the files have been cleared as virus-free by Mailscanner.
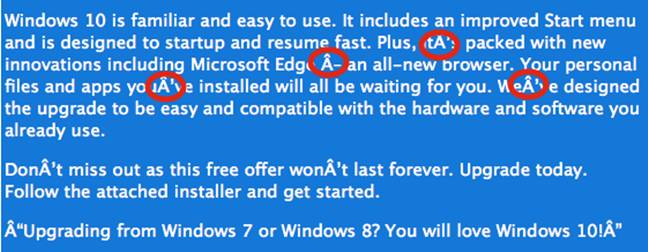
A 734KB attachment included in the emails claims to be a Windows 10 installer but actually contains the ransomware, which sets to work encrypting documents, media files, and anything else that might be useful to the hapless people who double-click on it. Analysis of the source code is ongoing, but the elliptic curve encryption algorithm used looks sound.
“I suspect this one is going to be an absolute bastard to deal with because they use good asymmetric encryption,” Craig Williams, security outreach manager of Cisco’s Talos team told The Register.
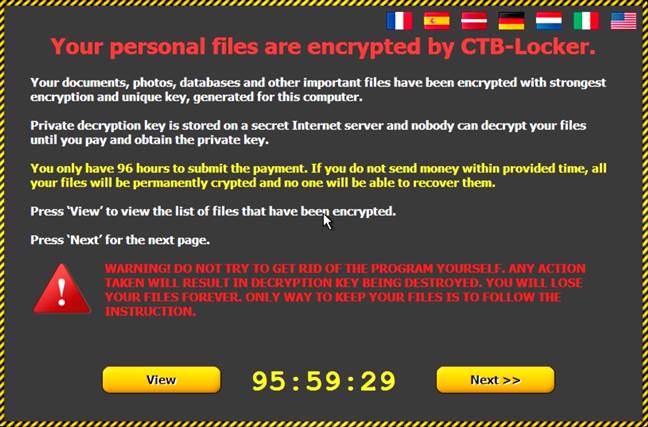
The ransomware is also unusual in a number of ways. It asks for the customary decryption charge in Bitcoin but only gives the user 96 hours to respond, which is a shorter window than is typical of similar malware. It also wants victims to respond via a Tor connection and provides instructions on how to use the protocol.
Williams told The Reg that it also demonstrates its efficacy by showing a complete list of encrypted files and offering to decrypt five of them for free.
“If you look at malware like Cryptolocker, it has built a market for itself because people know that if they pay they will get their files back,” Williams explained. “CTB-Locker is doing the same thing by proving to people they can do what they say they can do.”
Williams also said the malware was “unusually chatty,” sending back large amounts of data to command and control servers via hard-coded IP addresses. He speculated this could mean the malware is mining a victim’s files for stuff that looks useful.
Cisco has already built CTB-Locker countermeasures into its anti-malware software, and other vendors are developing antivirus signatures to block it, too. Williams said the initial campaign has been relatively small so far but, if enough people fall for the scam and pay up, the attackers could scale up their efforts.
“If you pay the attacker in Bitcoin then it’s a very smooth funding stream; the money goes directly to paying the [malware] development team,” he said. “That’s why we’re seeing such a fast development cycle in ransomware.”
Williams will present a talk on ransomware and other malware variants at next week’s Black Hat conference in Las Vegas.