Crowti ransomware spike
In a blog post dated 28/10/2014, Microsoft has warned of an uptick in the rate of detection of Crowti ransomware. According to the post, 71% of affected users were in the US, with Australia taking up second place with 11% of users.
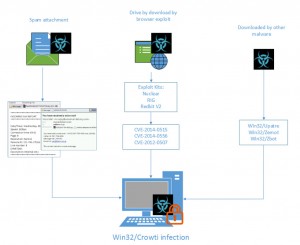
As per Figure A, one of the ways Crowti is spread is via spam email. The email contains an attachment (usually a zip file), which if opened and run will install the malware. Microsoft has listed a number of attachment names used by the spam email to lure the user into opening the attachment. The names used include Invoice, VOICE, document, etc.
If Crowti is successful, a ransom message is displayed informing the user that their files have been encrypted. Crowti points the user to a website where they can pay a ransom in Bitcoin. The message also informs the user to not bother looking for a solution “because they do not exist”. The recommendation from Microsoft is to not pay the ransom. Affected users may need to restore their files from a backup. Microsoft also recommends performing a full system scan.
Other methods of attack have also been observed using old vulnerabilities in Adobe Flash and Java. All of the vulnerabilities being exploited by Crowti have been patched.
As we often say on these pages, ensuring software is up to date with patching is one method of protection. Ensuring you have a good Anti Virus solution is another. Email Filtering is another component that can be used to stop malware before it even gets to a PC. Email Filtering can be particularly effective in this regard; the files never reach a user’s PC or Inbox; they are stopped and quarantined by the filtering program.
Above all, exercise care if you receive an email with an attachment or a link to a website. Ensure that the email is valid first before opening it. Check links before clicking; don’t login if the site address is even slightly different to what is expected.
Scott Reeves
MailShark
Free anti-spam service
Free email filter service