Stegosploit Future of Steganography Hide Code in Images
“A good exploit is one that is delivered with style”
The line reads in the report released by Net-Square CEO Saumil Shah at Hack in the Box Conference at Amsterdam this year. Saumil Shah is a hacker by profession. He has uncovered such a mind-boggling technique at the conference, which is definite to rule the hacking world in coming time. We all have heard about Steganography, Right? If not, let me tell you in simpler words, it is the art of hiding data (or exploit code). This was exploited in the wild continuously by hackers and cybercriminals to spread malware etc. The code was written in a file and file was used to merge with the image file of course.
So what’s different with Stegosploit? Yeah, a hell lot of difference is there! Images can directly be used to deliver exploit in the browser window, along with its decoding code. In other words, you can be tricked even without clicking a link or downloading a file, even if you just open a simple image, BAM! EXPLOIT TRIGGERED AUTOMATICALLY.
The Technique
Saumil explained JPG and PNG image encoding and encoding steps for Internet Explorer and Mozilla Firefox to use this exploit on. Browser exploits are already in the wild, so this technique boost up the web attacks online and we may see the rise in it exponentially. The technique surpasses the traditional Steganography, GIFAR concatenation, PHP/ASP webshells appending/embedding tags, XSS in EXIF data.
“Stegosploit lets you deliver existing BROWSER EXPLOITS using pictures”.
Yes, this is the power of this technique. Earlier you were only able to send messages or encoded things in pictures or videos, but now you can directly send exploits and add even the decoding code with the picture to explode at victim’s end!
Hacking with pictures, in style!
• Network traffic – ONLY image files.
• Exploit hidden in pixels.
– no visible aberration or distortion.
• Image “auto runs” upon load.
– decoder code bundled WITH the image.
• Exploit automatically decoded and triggered.
• …all with 1 image.
The above lines summarizes all.
Technical Details
According to the technique explained by Saumil, data is encoded at bit layers. Sharp visual distortion can be reduced significantly at lower levels.
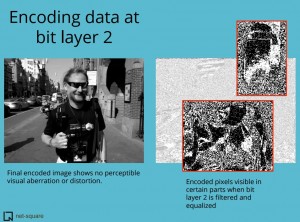
Encoding can be done on JPG and PNG files, and lot more supported formats. Decoding of data is as easy as explained by:
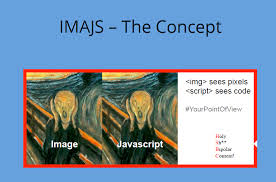
HTML5 can be used to read image pixel data using JavaScript and In-browser decoding of steganographically encoded images can be done with decoder already binded with the image. Shah took the already revealed browser vulnerabilities of Internet Explorer and Mozilla firefox and used them to create a new file format; IMAJS (Image + Javascript), that can run in the browsers and load malicious javascript code, rendering image alongside and the victim remains unnoticed.
“Packaged into a tool called Stegosploit, Shah takes known exploits Chrome, Safari, Explorer and other browsers supporting HTML 5 Canvas, and codes them into the but layers of an images’ pixels.These kind of files which Shah dubbed Imajs (image + JavaScript) load as JavaScript in a browser that render as images but also execute – two different kinds of content all embedded in one file.” continues iDigitalTimes.
Also, the anti-virus programs are not able to detect the file as they aren’t yet prepared for such advanced technique. Shah admitted that he may not be the first to find such thing, he just combined his two passions i.e. hacking and photography and started this project 5 years ago. He added that there may be someone who might have used creative thinking and done this “tough” job successfully. For In depth Technical details you can download the report published by the researcher.