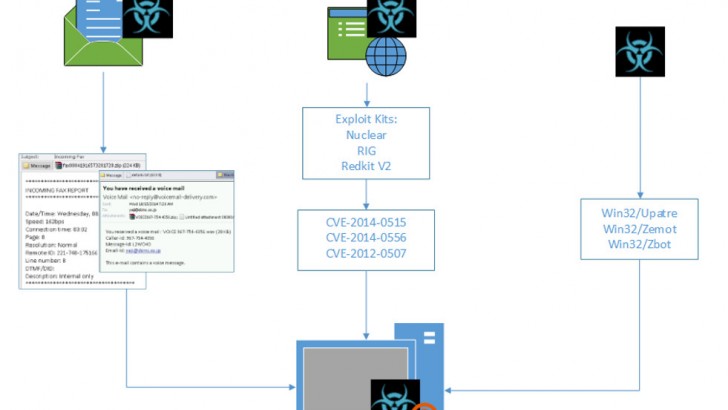
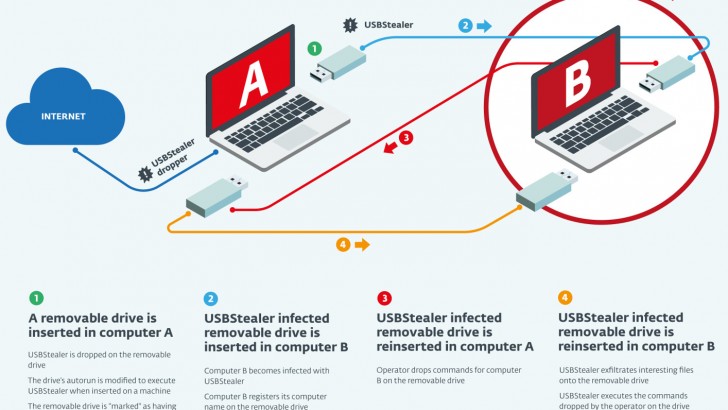
Crowti ransomware spike In a blog post dated 28/10/2014, Microsoft has warned of an uptick in the rate of detection of Crowti ransomware. According to the post, 71% of affected users were in the US, with Australia taking up second place with 11% of users. As per Figure A, one of the ways Crowti is…
Crowti ransomware spike